 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Let’s cut right to the chase: the number of severity of cyberattacks will explode in 2020. Cyberwarfare has now leveled the playing field in industry, in government, and in national defense: why spend ten or fifteen billion dollars on an aircraft carrier when you can disable it digitally? Why spend billions on new product R&D when you can hack into your competition’s strategic plans? Why not just phish around municipalities for a quick $100K?
Cyberwarfare is a cost-effective solution to all sorts of problems – and opportunities: cyberwar-fare is a revenue stream, a new business model, digital transformation with its own unique flavor. I’ve written about this before in several different ways, with all sorts of warnings. Not that I’m sounding a quiet alarm. The whole world is warning anyone who will listen about cyberwarfare. But regardless of inexplicably unheeded warnings, I predict 2020 will be different – much worse than it’s ever been. Why? Simply because it’s the cheapest, easiest, fastest and most effective form of warfare we’ve ever seen, and because cyberwarfare defenses are more vulnerable than they’ve ever been. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2012/05/21/visual-it-securitypart2-your-computer-as-a-possible-cyber-weapon/ https://www.scoop.it/t/securite-pc-et-internet/?tag=cyberwarfare https://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberwar...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Cyberwarfare is taking to the skies, aboard dronesHovering computers will make it increasingly possible to hack equipment that doesn’t connect directly to the internet. The drones: Cyberscoop rounded up a selection of drones that hack into networks. Take your pick: flying wiretaps for mobile networks, home-brew devices that turn off smart bulbs, or giants with 20-foot wingspans that meddle with Wi-Fi networks. What the experts say: “This market is about to blow up,” Francis Brown of thecybersecurity firm Bishop Fox told Cyberscoop. “Everyone is dumping money into this.” Why it matters: It’s often assumed that devices that don’t directly connect to the internet are relatively sheltered from attack. While it’s not straightforward, hovering a drone close to a vehicle or building could enable people to hack devices that use wireless communication but were once thought relatively safe. Hack backs: It’s also worth noting that drones, with wireless connections and precarious modes of travel, are highly susceptible to being hacked out of the sky, too. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet https://www.scoop.it/t/21st-century-innovative-technologies-and-developments/?&tag=Drones

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Notorious NSA contractor-turned-privacy advocate Edward Snowden warns the recent NSA hacks could have some really "messy" consequences. Notorious NSA contractor-turned-privacy advocate Edward Snowden today took toTwitter to discuss the details of yesterday’s ‘Equation Group’ hack. The Equation Group — allegedly an offshoot of the NSA — saw its defenses penetrated by a group calling itself ‘The Shadow Brokers.’ Eventually this data began to make its way online. The collected data is reported to be a cache of hack tools, known as binaries. According to Snowden, these tools are uploaded onto an NSA staging server as part of on-going operations to target and trace rival malware servers. The practice is known as Counter Computer Network Exploitation, or CCNE — a process that allows NSA hackers to steal tools used by foreign (or domestic rival) hackers in order to fingerprint them. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Shadow+Brokers

|
Scooped by
Gust MEES
|
Last Friday, a mysterious group by the name of “The Shadow Brokers” dumped what appeared to be some of the National Security Agency’s hacking tools online. There was some speculation as to whether the tools were legitimate. According to The Intercept, these tools are mentioned in documents leaked by NSA whistleblower Edward Snowden. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Shadow+Brokers

|
Scooped by
Gust MEES
|
The draft guide provides detailed example solutions using multiple products that achieve the same result, and instructions for implementers and security engineers, including examples of all the necessary components and installation, configuration and integration.
NIST notes that the draft guide also maps security characteristics to guidance and best practices from NIST and other standards organizations, and to North American Electric Reliability Corporation’s Critical Infrastructure Protection standards. The guide is modular and suitable for organizations of all sizes, including corporate and regional business offices, power generation plants and substations. They can adopt this solution or one that adheres to these guidelines in whole, or use the guide as a starting point for tailoring and implementing parts of a solution.
The draft guide can be found on the NCCoE Web site.
Learn more:
https://nccoe.nist.gov/projects/use_cases/idam

|
Scooped by
Gust MEES
|
Moskau/lngolstadt, 17. Februar 2015 Kaspersky Lab enttarnt die Cyberspionagegruppe „Desert Falcons“, die sich gegen verschiedene hochrangige Organisationen und Einzelpersonen im Nahen Osten richtet [1]. Damit konnten die IT-Sicherheitsexperten erstmals eine Gruppe von Cybersöldnern aus dem arabischen Raum enttarnen, die offenbar über das komplette Spektrum von Cyberspionagemitteln verfügt.
Die Gruppe startete ihre Aktivitäten bereits im Jahr 2011, seit dem Jahr 2013 werden Rechner infiziert. Den Experten von Kaspersky Lab zufolge erreichte die Kampagne ihren Höhepunkt zu Beginn des Jahres 2015 [2].

|
Scooped by
Gust MEES
|
More than one thousand energy firms are said to have been targeted by internet hackers, with particular interest in compromising industrial control systems.
There is no doubt that we have entered a new era of cybercrime, where countries are not just fighting the threat – but are also exploiting the internet for their own interests using the same techniques as the criminals.
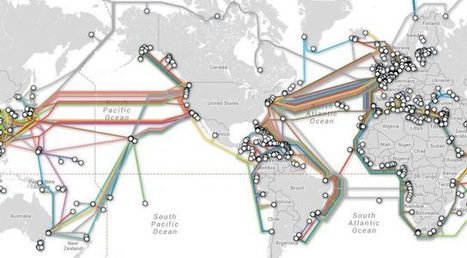
How does cyber warfare work? This question was originally answered on Quora by Andy Manoske. Simply put, cyber warfare is the use of hacking to conduct attacks on a target’s strategic or tactical resources for the purposes of espionage or sabotage.

|
Scooped by
Gust MEES
|
Sitting in an office in the Australian Security Intelligence Organisation’s Soviet-style building, which mirrors the Orwellian bunker one might imagine, Australia’s most experienced spy master, David Irvine, has a lot on his mind as he gazes over...

|
Scooped by
Gust MEES
|
DARPA postpones release of official solicitation. Officials at the Defense Advanced Research Projects Agency have decided to postpone briefings and the release of solicitation documents for Plan X, a widely-anticipated funding initiative that will lay the foundation for the government’s push into offensive computer warfare operations. “Due to an unanticipated and overwhelming response from industry and academia, DARPA has rescheduled the Plan X Proposers’ Day Workshop,” agency officials announced Sept. 5. Two sessions with researchers and defense contractors—one classified and one non-classified—originally were slated for Sept. 27, but have now been moved to Oct. 15 and 16. “The second day will be a repeat of the first day to accommodate the remaining attendees,” the notice said. The request for proposals, originally scheduled for release at the end of this month, is expected to be published in October instead. The surge of interest highlights a community emerging around offensive security technology. Plan X is a Pentagon initiative to develop computer architecture that monitors damage in “dynamic, contested, and hostile network environments,” adaptively defends against attacks, and performs “weapon deployment,” contracting documents indicate. The program is not funding malware or tools that hunt down vulnerabilities, but the resulting computer architecture will likely serve as the framework for their deployment. Read more: http://www.nextgov.com/defense/2012/09/pentagon-receives-overwhelming-response-plan-x-cyber-offensive/57961/
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
What is cyberwar?
At its core, cyberwarfare is the use of digital attacks by one country or nation to disrupt the computer systems of another with the aim of create significant damage, death or destruction.
What does cyberwarfare look like?
Cyberwar is still an emerging concept, but many experts are concerned that it is likely to be a significant component of any future conflicts. As well as troops using conventional weapons like guns and missiles, future wars will also be fought by hackers using computer code to attack an enemy's infrastructure.
Governments and nation states are now officially training for cyberwarfare: An inside look
Europe, Canada, USA, Australia, and others are now running training exercises to prepare for the outbreak of cyberwar. Locked Shields is the largest simulation and TechRepublic takes you inside.
Read More
Governments and intelligence agencies worry that digital attacks against vital infrastructure -- like banking systems or power grids -- will give attackers a way of bypassing a country's traditional defences. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2012/05/21/visual-it-securitypart2-your-computer-as-a-possible-cyber-weapon/

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Der Nachrichtendienst NSA ist offenbar Opfer eines Hackerangriffs geworden. Bereits 2013 erbeutete Überwachungsprogramme wurden jetzt im Internet veröffentlicht. Edward Snowden vermutet russische Hintermänner. Für die NSA könnte der Hack unangenehme Folgen haben.

|
Scooped by
Gust MEES
|
This is surely no frivolous hacker feud, but an incredibly sophisticated attack on the US cyber-security infrastructure — even though it was meant to look like it was carried out by Guy-Fawkes-mask-wearing ideological warriors, at least a bit. It even features a quasi-illiterate intro/rant railing against “the elites.” It’s a familiar refrain in an American political season dominated by anti-establishment politicians, and it fits well with the stereotype of the libertarian hacker — but it also seems to want to convince these elites not to support the sort of offensive hacking on display in their leak. Emphasis added:
We want make sure Wealthy Elite recognizes the danger cyber weapons, this message, our auction, poses to their wealth and control. Let us spell out for Elites. Your wealth and control depends on electronic data. You see what “Equation Group” can do. You see what cryptolockers and stuxnet can do. You see free files we give for free. You see attacks on banks and SWIFT in news. Maybe there is Equation Group version of cryptolocker+stuxnet for banks and financial systems? If Equation Group lose control of cyber weapons, who else lose or find cyber weapons? If electronic data go bye bye where leave Wealthy Elites? Maybe with dumb cattle? Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Shadow+Brokers http://www.scoop.it/t/securite-pc-et-internet/?tag=NSA

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Russian hacker spies are attacking energy companies. It's the latest sign the Cold War has gone cyber.

|
Scooped by
Gust MEES
|
Britain is building an army to wage war by hurling computer hackers at its enemies. Defence Secretary Philip Hammond said the country is recruiting "hundreds" of hackers at a cost of up to £500 mil...

|
Scooped by
Gust MEES
|
What is the consequence of cyber warfare slowly becoming increasingly common? The “happy hacker” of the 80s and 90s, he said, is long gone. Instead, we now have to deal with criminals who try to make money from their malware and botnets, hacktivists who try to protest and governments attacking their own citizens and other governments for espionage and full-scale cyber warfare.
As for cyber warfare in general, one thing Hypponen especially stressed is the difference between cyber espionage and cyber warfare. Spying, said Hypponen, is not warfare. “Warfare is something different,” he said. “It’s when you start using malware, viruses and backdoors to target our critical infrastructure.” Today, he argued we are seeing the very first stages of a global cyber arms race. We are now seeing many other governments besides U.S. and Israel jump on the same bandwagon and now that other countries see that these attacks are successful, they want to jump on the bandwagon, too.

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...































Let’s cut right to the chase: the number of severity of cyberattacks will explode in 2020. Cyberwarfare has now leveled the playing field in industry, in government, and in national defense: why spend ten or fifteen billion dollars on an aircraft carrier when you can disable it digitally? Why spend billions on new product R&D when you can hack into your competition’s strategic plans? Why not just phish around municipalities for a quick $100K?
Cyberwarfare is a cost-effective solution to all sorts of problems – and opportunities: cyberwar-fare is a revenue stream, a new business model, digital transformation with its own unique flavor. I’ve written about this before in several different ways, with all sorts of warnings. Not that I’m sounding a quiet alarm. The whole world is warning anyone who will listen about cyberwarfare. But regardless of inexplicably unheeded warnings, I predict 2020 will be different – much worse than it’s ever been. Why? Simply because it’s the cheapest, easiest, fastest and most effective form of warfare we’ve ever seen, and because cyberwarfare defenses are more vulnerable than they’ve ever been.
Learn more / En savoir plus / Mehr erfahren:
https://gustmees.wordpress.com/2012/05/21/visual-it-securitypart2-your-computer-as-a-possible-cyber-weapon/
https://www.scoop.it/t/securite-pc-et-internet/?tag=cyberwarfare
https://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberwar...